Israel’s National Cyber Directorate said Sunday that it had warned the Israeli internet hosting company breached by a hacker group linked to Iran over the weekend that it was vulnerable to an attack.
Libi Oz, a spokeswoman for the government-funded agency, said her office warned CyberServe “several times.”
CyberServe did not respond for a request to comment, but said in a statement Saturday that it had been dealing with “an Iranian cyber terror event.”
“From the moment we got warning on the issue from the National Cyber Directorate, even before the incident, we cooperated fully and fulfilled all the directorate’s guidelines,” it said.
The Black Shadow hacking group, which in recent days has been leaking personal information from Israeli websites hosted by CyberServe, demanded on Sunday a ransom payment of $1 million in digital currency to stop the online leak of personal information from the Israeli LGBT site Atraf.
“If we have 1 Millions $ in our wallet in the next 48 hours, we will not leak this information and also we will not sell it to anybody,” Black Shadow wrote on Telegram.
On Saturday, the group dumped tens of thousands of records online from the various sites it had penetrated, including 1,000 user profiles from Atraf. The leaked records included users’ HIV status, sexual orientation, and unencrypted passwords.

A person speaks on their phone during an annual Gay Pride Parade in Jerusalem, on June 3, 2021. (Olivier Fitoussi/ Flash90)
The hackers said on Sunday that the information leaked online so far represented just 1 percent of the data acquired in the breach.
Ran Shalhavi, CEO of The Aguda — The Association for LGBTQ Equality in Israel, said his organization had extended its emergency hotline hours to deal with a flood of worried callers.
“They are exposed, and if they are in the closet, they are exposed to situations they never knew before,” he said, adding that the association was working with different groups to “reduce damage.”
Cyber intelligence researcher Ohad Zaidenberg said the breach appeared to be linked to a hack of Israeli insurance firm Shirbit last year, also claimed by Black Shadow, as well as an attack in March on Israeli insurance company KLS Capital Ltd.
“Now they are doing something relatively similar,” Zaidenberg said. “We know that attack on Shirbit was Iranian, and therefore we can say, if it’s the same attacker and that attack was Iranian, this attack is Iranian.”
Israeli media said Black Shadow is a group of Iran-linked hackers who use cyberattacks for criminal ends.
The group breached Israel’s Shirbit insurance firm in December last year, stealing data. It demanded a $1 million ransom and began leaking the information when the firm refused to pay.
Keren Elazari, a cybersecurity expert and researcher at Tel Aviv University, agreed that the attack appeared to be Iranian.
“A big part of the hacks we’ve seen is not about ransom,” she said. “It’s about embarrassing Israeli companies, embarrassing Israeli citizens.”
She said the pandemic had opened new vulnerabilities for Israeli firms, as working from home offered less cybersecurity and has “multiplied the opportunity for attacks.”

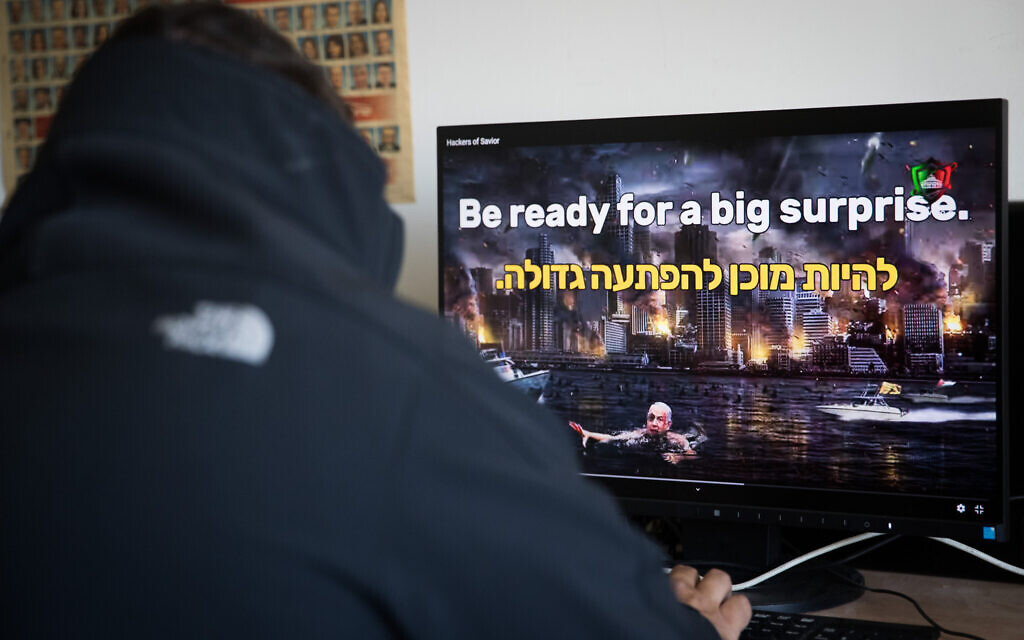
Illustrative. Hacking, hackers, ransomware, and a cybersecurity attack. (solarseven; iStock by Getty Images)
The cyberattack also hit websites, including of Israeli public transportation companies Dan and Kavim, a children’s museum and public radio online blog, with the sites still available to users by midday Sunday. The attack also targeted the tourism company Pegasus, and Doctor Ticket, a service that could have sensitive medical data, according to Hebrew media.
The new attack comes after an unprecedented, unclaimed cyberattack wrought havoc on Iran’s gas distribution system this week, which Tehran officials have blamed on Israel and the United States.
Iran and Israel have been engaged in a so-called “shadow war,” including several reported attacks on Israeli and Iranian ships that the two have blamed on each other, as well as cyberattacks.
In 2010, the Stuxnet virus — believed to have been engineered by Israel and its ally the US — infected Iran’s nuclear program, causing a series of breakdowns in centrifuges used to enrich uranium.
https://www.timesofisrael.com/israel-cyber-authority-says-it-warned-hosting-company-it-was-vulnerable-to-hack/