Researchers from universities in Israel, Australia and France have discovered a device identification technique that is based entirely on GPU fingerprinting.
Fingerprinting in the computing world refers to the identification of devices or users. It may be used individually or in combination with other tracking techniques.
Fingerprint attempts may use one or multiple factors retrieved from a user’s device to track users online. At least some data is revealed automatically when users connect to websites using modern web browsers, others may be retrieved using scripts that run on the website itself.
Connecting to sites may reveal information about the operating system, screen size or language that is used on the device. Some of these factors may change, e.g. the size of the browser window, while others may not.
Some web browsers, e.g., Firefox or Brave, include anti-fingerprinting options, but these address only common forms and not all methods that can be used potentially for that purpose.
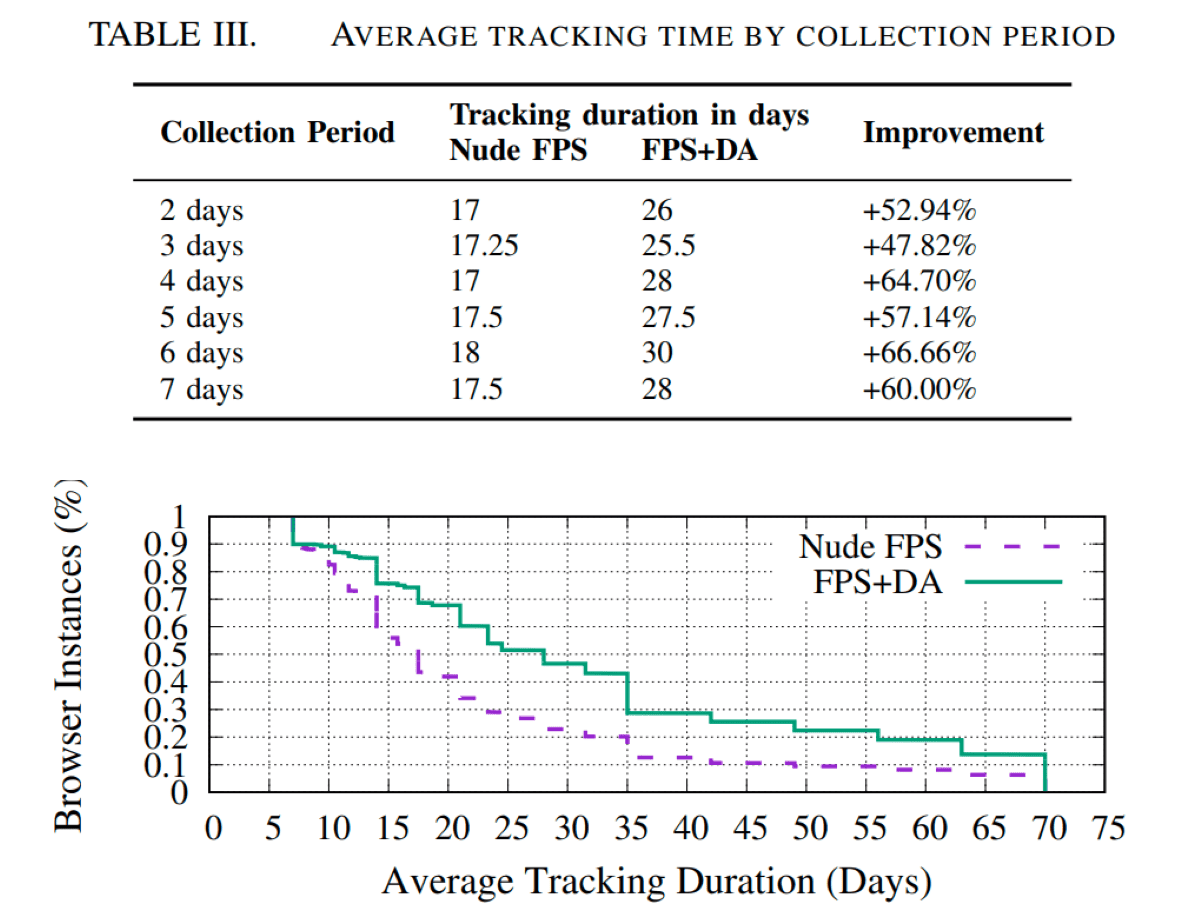
The GPU fingerprinting technique that the researchers discovered relies solely on the graphics processing unit. The technique may be used to extend the tracking time of other fingerprinting methods by up to 67% according to the research paper.
To put this into perspective: the average tracking time according to the researchers is between 17 to 18 days. The GPU fingerprinting method that the researchers discovered extends this to a period between 25.5 and 30 days; a significant increase.
The researchers ran experiments on 2500 unique devices using the technique. They developed two methods, both of which use the Web Graphics Library (WebGL), which is supported by all modern web browsers.
The researchers describe how the technique, which they call DRAWNAPART, works in the research paper:
By fingerprinting the GPU stack, DRAWNAPART can tell apart devices with nominally identical configurations, both in the lab and in the wild. In a nutshell, to create a fingerprint, DRAWNAPART generates a sequence of rendering tasks, each targeting different EUs. It times each rendering task, creating a fingerprint trace. This trace is transformed by a deep learning network into an embedding vector that describes it succinctly and points the
adversary towards the specific device that generated it.[..] by using short GLSL programs executed by the GPU as part of the vertex shader (cf. section II-B). We rely on the mostly predictable job allocation in the WebGL software stack to target specific EUs. We observe that, when allocating a parallel set of vertex shader tasks, the WebGL stack tends to assign the tasks to different EUs in a non-randomized fashion. This allows us to issue multiple commands that target the same EUs.
Finally, instead of measuring specific tasks, we ensure that the execution time of the targeted EU dominates the execution time of the whole pipeline. We do so by assigning the non-targeted EUs a vertex shading program that is quick to complete, while assigning the targeted EUs tasks whose execution time is highly sensitive to the differences among individual EUs. A
Both onscreen and offscreen methods have been created to address different use cases. The onscreen method is faster but requires more resources, the offscreen method takes longer to deliver results but it is more resource friendly.
The researchers note that countermeasures may block the successful creation of fingerprints using the method. Tor Browser, with its “minimum capability mode” blocks the use of an API that the attack relies on by default. WebGL may also be disabled in other browsers to prevent the attack, but at the cost of potential usability or accessibility issues. Script blocking can be effective, but only if scripts are blocked by default and allowed manually by the user.
Check out a study on the effectiveness of anti-fingerprinting measures here.
You can check out the full research paper linked above for additional details.
Now You: do you use anti-fingerprinting protections? (via Bleeping Computer)
Summary
Article Name
Your device’s GPU may be used for fingerprinting purposes
Description
Researchers from universities in Israel, Australia and France have discovered a device identification technique that is based entirely on GPU fingerprinting.
Author
Martin Brinkmann
Publisher
Ghacks Technology News
Logo

Advertisement



